MedTech Cybersecurity Starts Earlier Than You Think: What Every Founder Needs to Know
In the early days of medical technology, "safety" meant mechanical reliability and sterile materials. Today, a life-saving ventilator or a precision insulin pump is essentially a specialized computer running on a network. While connectivity has revolutionized patient outcomes, it has also opened a digital back door to the operating room.
This shift became a startling reality in 2015 when the FDA issued its first-ever safety alert based purely on cybersecurity. The agency warned hospitals that the Hospira Symbiq Infusion System (FDA Safety Communication here) contained vulnerabilities that could allow an unauthorized user to remotely hijack the device and change the dosage a patient received.
As the line between healthcare and hardware continues to blur, cybersecurity can no longer be a final "check-the-box" activity before a regulatory submission. It is now the very foundation of patient safety.
Why Early Cybersecurity Matters
We often talk about the "Golden Hour" in emergency medicine—that critical window where intervention has the highest impact. In product development, your "Golden Hour" is the design phase. If you wait until your prototype is finished to think about security, you have already missed your best chance to protect the patient. You aren't just behind; you are building on a foundation of "Technical Debt" where the interest is paid in patient risk. Retrofitting security into a finished device is like trying to install a life-support system after the surgery is over—it’s expensive, invasive, and rarely as effective as a native solution.
Beyond the engineering headache, the legal landscape has shifted to reflect these life-and-death stakes. Under Section 524B of the FD&C Act, the FDA now treats a lack of cybersecurity as a fundamental device defect. They have the authority to refuse your submission at the door if you cannot prove your "cyber device" was built within a Secure Product Development Framework (SPDF). This isn't just a hurdle for the U.S. market; by tackling these hard conversations on day one, you are ensuring your device survives the transition to EU MDR and the strict privacy scrutiny of GDPR.
Starting early isn't about "checking a box" for a regulator; it’s about writing the ending of your story before you start the first chapter. It ensures you are asking the right questions while the answers are still cheap to implement. By the time your device reaches a patient’s bedside, its security destiny is already written—starting today ensures you’re writing a story of safety, not a cautionary tale of "what if."
The Exploding Threat: Cybersecurity in Healthcare
The healthcare sector is a "perfect storm" for cybercriminals, and the numbers backing this up are staggering. According to research published in the Journal of Clinical Monitoring and Computing (PMC10123010), the global cost of cyberattacks on the healthcare sector was projected to hit $6 trillion in 2021, a 100% increase from just six years prior. In the U.S. specifically, a single healthcare data breach now costs an average of $7.13 million—nearly double the global average of any other industry.
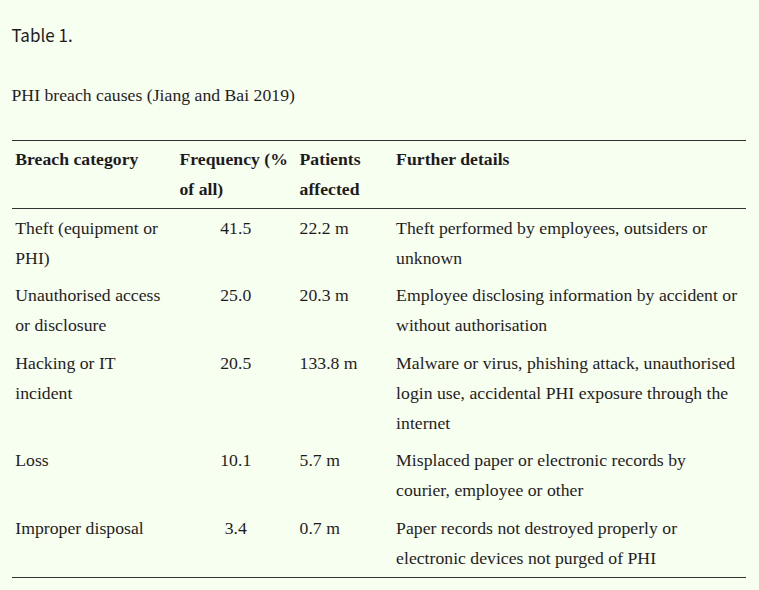
PHI Breach Causes (Jinag and Bai 2019)
Why are hackers so obsessed with hospitals? It’s a matter of "ROI." Patient records (Protected Health Information or PHI) are the "crown jewels" of identity theft. Because a medical record contains permanent data—social security numbers, genetic info, and chronic history—it cannot be "cancelled" like a credit card. Consequently, these records are worth ten times more than credit card numbers on the dark web, often fetching up to $1,000 per record.
But for medical device creators, the threat isn't just a financial ledger; it's a safety crisis. The research highlights several "nightmare scenarios" that move beyond data theft into physical harm:
The "IoMT Window": Every connected ventilator, anesthesia machine, and infusion pump is a potential "window" into the hospital’s entire Electronic Medical Record (EMR) system.
Signal Interference: A hacker doesn't need to steal data to kill; they only need to delay a telemetry signal or silence a cardiac alarm. If a nurse doesn't hear a heart monitor because the network is lagging under a DDoS attack, the result is the same as a mechanical failure.
Malicious Imaging: Researchers have already demonstrated the ability to use AI to maliciously add or remove tumors from 3D medical imagery (CT/MRI scans) in real-time, leading to misdiagnosis or unnecessary, dangerous surgeries.
The Post-COVID Attack Surface: The pandemic triggered a 600% increase in phishing attacks as healthcare workers shifted to "unsecured" home networks. This expanded the "threat surface" from the locked-down hospital server room to the chaotic world of home Wi-Fi routers.
In this landscape, a device without robust encryption and authentication isn't just a tool; it's a high-value target that puts the patient's identity—and their life—at risk.
Not Everything Needs to Be “IoMT” — Design with Purpose
The "Internet of Medical Things" (IoMT) is a powerful trend, but it is not a requirement for innovation. In fact, in a world where every connection point is a potential vulnerability, the most sophisticated design choice you can make is often the "Power of No."
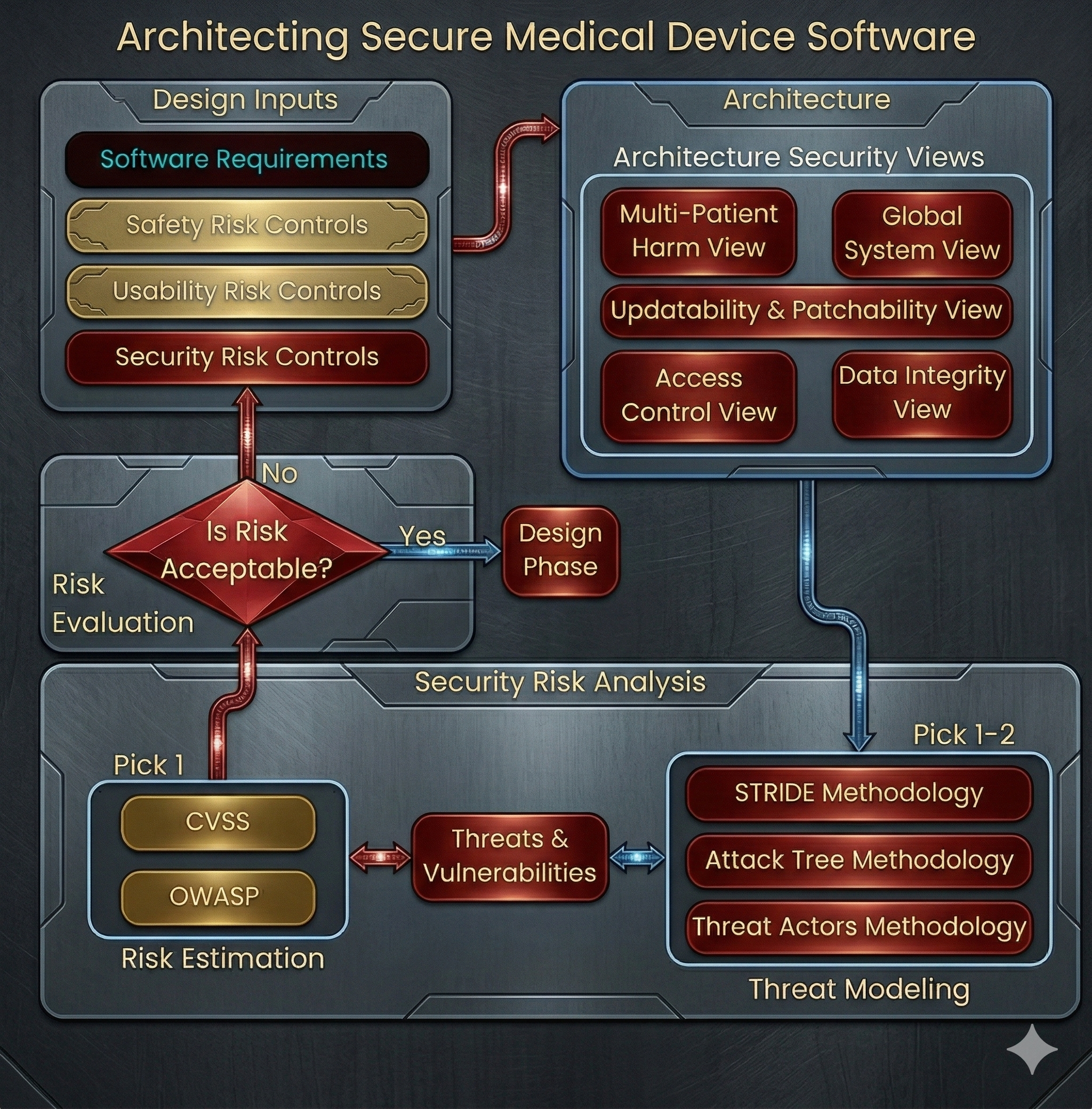
Architecting Secure Medical Device Software
As a founder, you must ask the hard question: Does this device truly need to be online? Designing with purpose means practicing "least privilege" in your hardware architecture. If a device only needs to sync data once a day, it shouldn’t have a persistent 24/7 connection. If it doesn't need to be controlled remotely, don't build a remote-control API. Security-by-design often means having the discipline to say "no" to unnecessary features that increase the risk profile without adding significant clinical value.
To lead your engineering team through this, use this "Purpose-Driven Design Checklist" as your internal gauntlet before a single circuit board is printed:
[ ] The "Why Connect?" Audit: Can the device perform its primary clinical function without an internet connection? If yes, the connection should have a physical "kill switch" or "Air Gap" capability.
[ ] Least Privilege Connectivity: Does it need a 24/7 "heartbeat," or can it use Store and Forward? (Collect data locally, wake up the radio for 30 seconds to sync, and go back to sleep).
[ ] No Default Passwords: Does the device ship with a unique, non-repeating password for every unit? Hardcoded "Admin/Admin" logins are the #1 way botnets take over medical hardware.
[ ] Secure Boot & Firmware Integrity: Can the device verify its own software hasn't been tampered with before it starts up? If a hacker loads malicious code, the hardware should refuse to run.
[ ] Physical Port Lockdown: Are there exposed USB or Ethernet ports? If a port is only for "Service/Maintenance," it should be internally disconnected or protected by a physical tamper-evident seal.
[ ] Encryption at Rest and in Transit: Is the data scrambled both while sitting on the device and while flying through the air? Standard AES-256 encryption is the bare minimum for 2026.
[ ] The "Zeroize" Protocol: If the device is stolen, do you have a way to remotely wipe the sensitive patient data without "bricking" the life-saving hardware?
By sticking to this checklist, you aren't just building a "secure" device; you're building a resilient one. You’re ensuring that when a vulnerability is inevitably found in a common Wi-Fi chip, your device isn't the low-hanging fruit that brings down a hospital network.
But I’m Not a Technical Founder—How Can I Lead This?
You don’t need to be a cryptographer to lead a secure MedTech company; you need to be a culture-setter. Cybersecurity is a management challenge as much as a technical one. If you treat security as a "nerd problem" for the dev team to solve in the basement, you’ve already lost. As a founder, your job is to ensure that the "Safety and Security" budget is never the first thing to be cut when a deadline looms.
Leading this charge doesn't require a computer science degree—it requires asking the right questions in the boardroom:
"Show me our SBOM:" Don't just ask if the software is "good." Ask to see the Software Bill of Materials. This is your ingredient list. If a major vulnerability like Log4j or a new Wi-Fi chip exploit breaks the news, you need to be able to ask your CTO, "Are we in this list?" and get an answer in minutes, not weeks.
"How do we fail safely?": In MedTech, "Security" isn't just about blocking hackers; it's about Resilience. Ask your engineers: If the network goes down or a hacker floods the device with data, does it shut off (dangerous) or does it revert to a basic, manual life-saving mode (safe)?
"What is our SOC 2 status?": Even if you aren't technical, you understand trust. Investing in SOC 2 compliance is a roadmap for how your organization handles data, background checks, and incident response. It is the "gold standard" that tells hospitals and investors that you have grown-up processes in place.
"Are we hiring for a 'Security Mindset'?": When interviewing, don't just look for fast coders. Look for engineers who naturally talk about "edge cases" and "failure modes." You want the person who asks, "What happens if this message is intercepted?" before they even start writing the feature.
Closing Thought
In the world of MedTech, we often talk about the "Golden Hour" in emergency medicine—the window where intervention has the highest impact. In cybersecurity, the "Golden Hour" is the design phase. By the time a device reaches a patient’s bedside, its security destiny is already written.
The FDA’s shift toward Section 524B and the 2026 QMSR alignment aren't just more red tape; they are the industry's way of catching up to a reality where a line of code can be as lethal as a malfunctioning heart valve. As a leader, your mission is to ensure that when your device is finally in the hands of a clinician, you aren't just delivering a tool—you’re delivering a promise of safety. Let’s make sure we’re writing stories of resilience, not cautionary tales of "what if."
About Landi Industries We help teams navigate the complexities of product development by sharing the hard-earned lessons of hardware engineering. From structural design to system architecture, our goal is to provide the roadmap for turning ambitious concepts into reliable physical products.
Stay in the Loop:
The Landi Handbook (Beehiiv): Our primary deep-dive newsletter for tactical engineering advice and hardware development strategies.
LinkedIn Newsletter: A medical-focused newsletter breaking down complex technical topics for non-technical professionals and stakeholders.
YouTube: Visual guides and technical walkthroughs covering the realities of the product development process.
Medium: Long-form articles exploring the deep "why" behind successful hardware and system design.
Work With Us: Need expert help with your next build? See our full range of services at LandiIndustries.com